Eliminate Standing Access, Enforce Just-In-Time Security
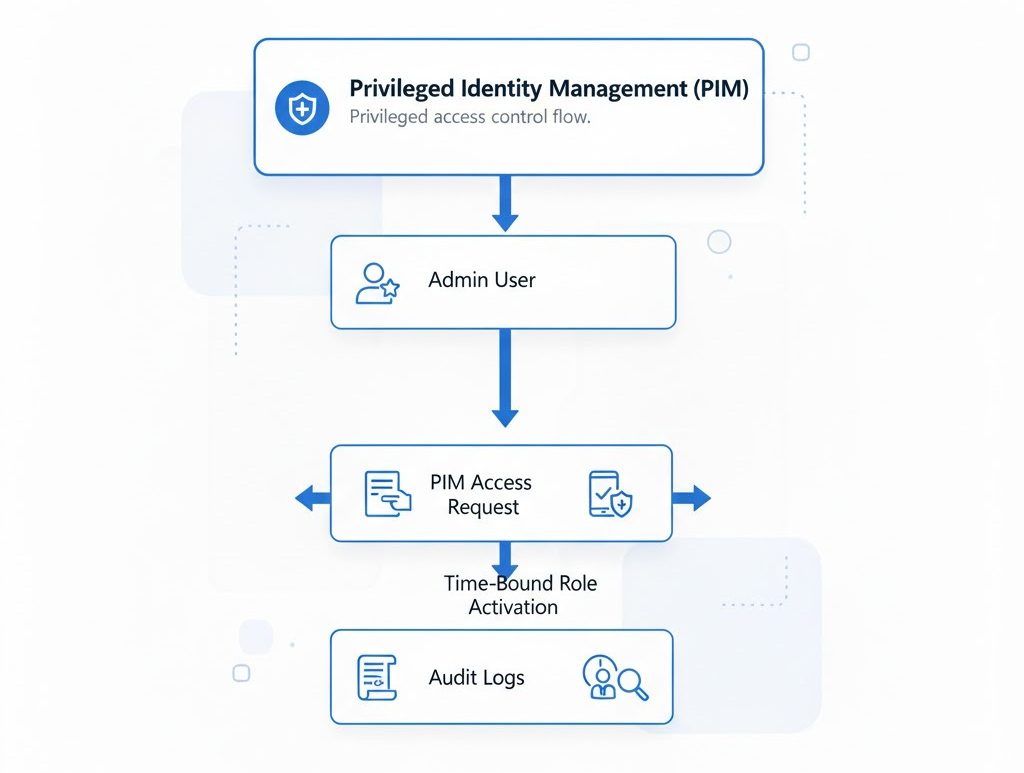
We implement Microsoft Entra PIM to secure your most sensitive administrative roles. By moving away from permanent “standing” access to a Just-In-Time (JIT) model, we significantly reduce the attack surface. This ensures that high-level permissions are only active when needed, minimizing the risk of credential compromise and internal privilege abuse.

Privileged role eligibility design

Just-in-time access configuration

Approval, justification, and access workflows

Privileged access auditing and reportin

Operational guidance for admin access management
Powered by Profecient WordPress Themes
Copyright © 2026