Services That Power This Solution
- Microsoft Entra ID Implementation & Hardening
- Identity Security Assessments
- Joiner–Mover–Leaver (JML) Governance
- Identity Troubleshooting & Incident Support
Outcomes
- Reduced credential-based attacks
- Consistent access enforcement
- Faster onboarding and offboarding
- Improved audit readiness
- Reliable employee access experience
Secure Hybrid Identity for Cloud Migration
Ensure seamless identity integration between on-premises Active Directory and Microsoft Entra ID. Hybrid identity environments introduce complexity that, if mismanaged, leads to authentication failures, device trust issues, and security gaps. IdentityOpsIAM designs and stabilizes hybrid identity architectures that support secure cloud adoption without disrupting business operations. The Business Challenge
Common hybrid identity challenges include:
- Unreliable sign-in experiences
- Device registration inconsistencies
- Confusing authentication flows
- Identity synchronization failures
- Security blind spots between environments
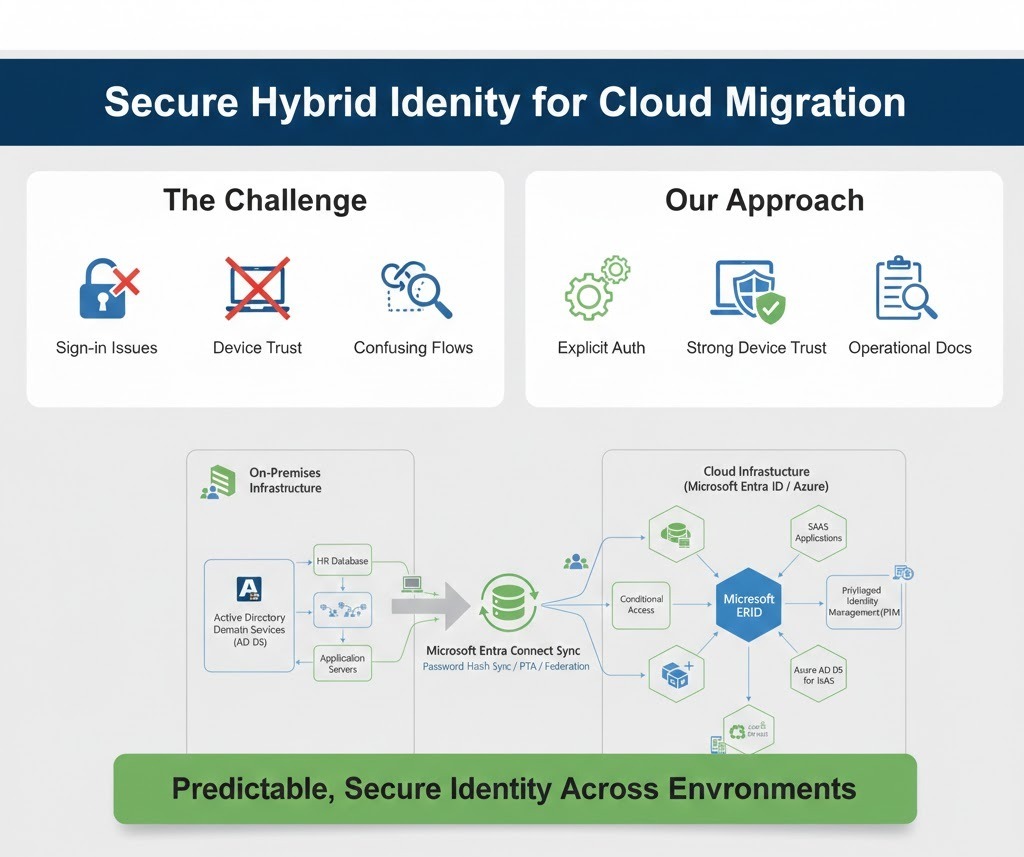
Secure Your Cloud Migration with Robust Hybrid Identity
Hybrid identity environments can be complex. We simplify integration, mitigate risks, and ensure stable authentication flows as you transition to the cloud.”
Services That Power This Solution
Outcomes
We design and implement Microsoft Entra ID environments that meet enterprise security, governance, and operational requirements. This service ensures that identity foundations are configured correctly from the start and aligned with Microsoft-recommended best practices.
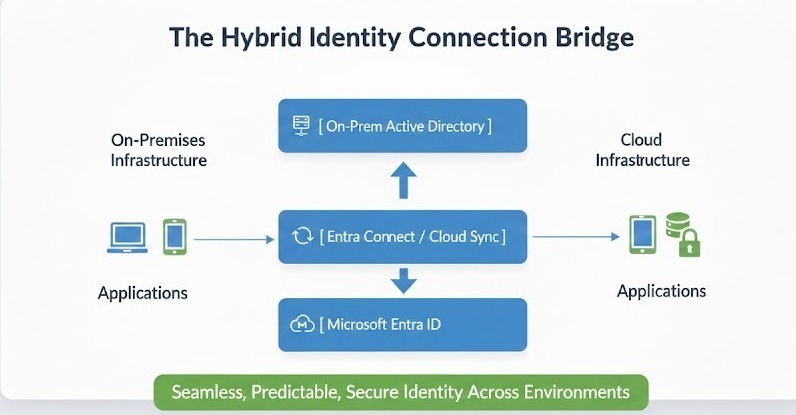
For organizations operating both on-premises Active Directory and cloud services, we design and stabilize hybrid identity architectures. This ensures identities, devices, and access policies function consistently across environments.
Transform Your HR Strategy with Our Affordable Pricing Plans
Basic Plan
$23/per month
Premium Plan
$49/per month
Enterprise Plan
$137/per month
Ultimate Plan
Custom Quote
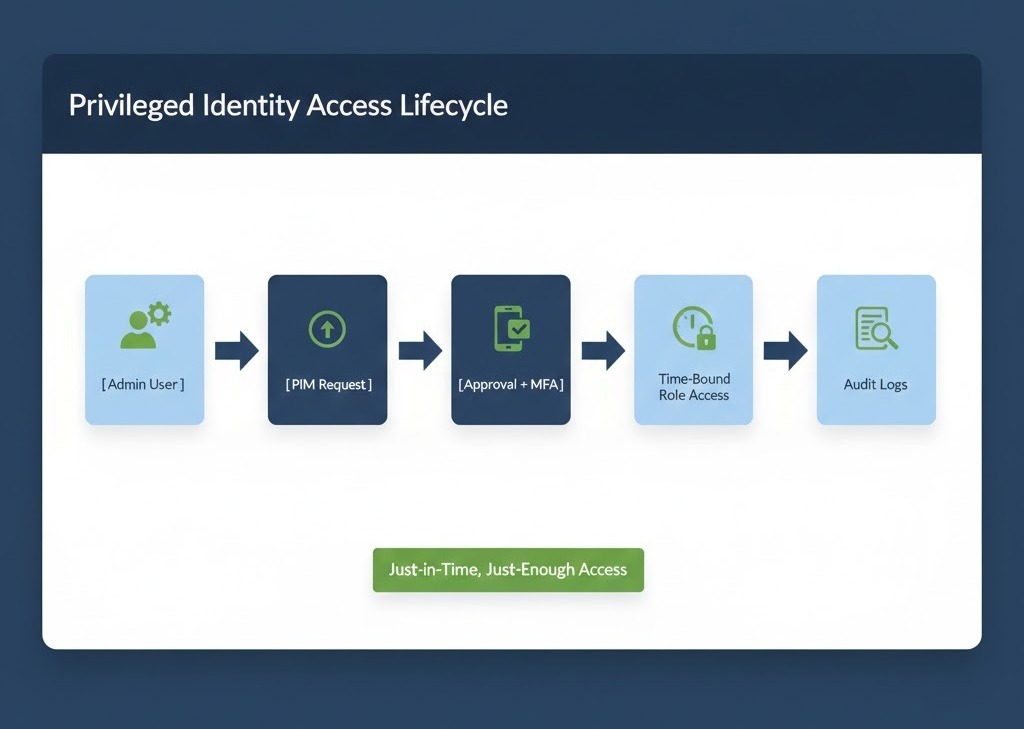
Privileged Access & Administrator Security
Secure Privileged Access Across Your Organization Eliminate standing administrative access and reduce the risk of identity-based attacks. Administrative identities are a primary attack target and a key focus for auditors. Without strong governance, privileged access creates unacceptable risk. IdentityOpsIAM helps organizations control, monitor, and govern privileged access using Microsoft Entra Privileged Identity Management (PIM).
Services That Power This Solution
Outcomes
Secure Privileged Access Across Your Organization
Eliminate standing administrative access and reduce the risk of identity-based attacks. Administrative identities are a primary attack target and a key focus for auditors. Without strong governance, privileged access creates unacceptable risk. IdentityOpsIAM helps organizations control, monitor, and govern privileged access using Microsoft Entra Privileged Identity Management (PIM).
Service & Outcomes
- Privileged Identity Management (PIM)
- Microsoft Entra ID Hardening
- Identity Security Assessments
- Reduced privilege exposure
- Improved audit results
- Strong accountability for admin access
- Alignment with Zero Trust principles
Ready to Optimize Your Hybrid Identity?
Don’t let identity complexities derail Yun cloud migration experts ensure a secure and stable transition.
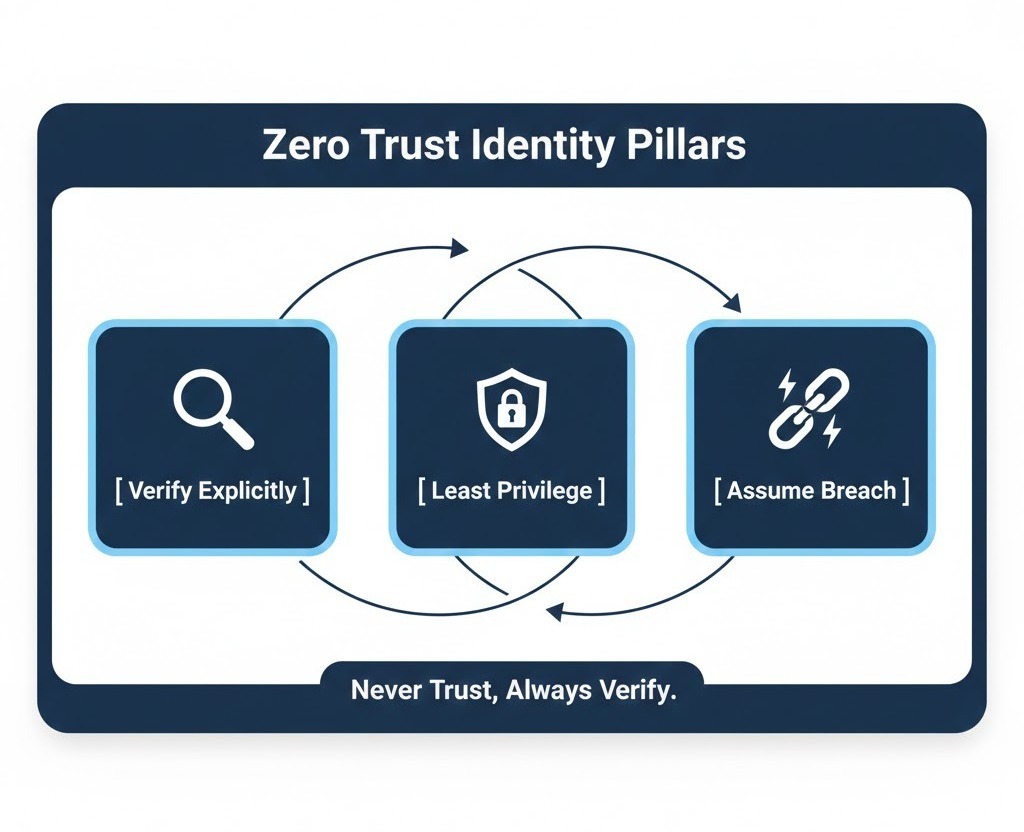
Zero Trust Identity for Microsoft Environments
Protect identities using continuous verification, least privilege, and strong governance. Zero Trust begins with identity. IdentityOpsIAM helps organizations design identity architectures that enforce Zero Trust principles across users, devices, and administrators.
Services That Power This Solution
• Conditional Access
• Privileged Identity Management (PIM)
• Identity Security Assessments
• JML Identity Governance
Our Zero Trust Identity Approach
We design identity systems that:
• Verify explicitly
• Enforce least privilege
• Assume breach
• Continuously validate access signals
Outcomes
• Reduced blast radius of attacks
• Strong access governance
• Improved compliance posture
• Secure and resilient identity platform
Powered by Profecient WordPress Themes